Remote nowBooking an appointment
Summary




Home Office Checklist - Corona crisis becomes surveillance scandal 2.0
After the advantages of home office became clear, one should still not rush anything.
Because even if the whole world feels that it is necessary to slow down the spread of the corona virus, there are unfortunately people, organizations and even authorities and companies who take advantage of this situation.
The corona crisis has stirred up many minds. Many entrepreneurs are interested in a quick solution, forgetting the daily dangers of digital data processing that existed before the corona virus. People's privacy is sometimes trampled underfoot.
Corona crisis gives authorities reason to monitor
Edward Snowden recently spoke personally about the Corona crisis. The whistleblower warns against surveillance measures introduced in the wake of the corona virus, which could lead to this regulation being adopted permanently in legislation.)
I personally found Edward Snowden's interview on the current corona crisis very exciting.
In this context, I do not wish to offend any company and will deliberately refrain from mentioning names. But I would like to take this opportunity to ask you to critically examine the situation and reports!
Natürlich wird aktuell kein Unternehmen zugeben, dass sie Kundendaten an Behörden oder Dritte weitergeben werden. Die Unternehmen und Behörden selbst haben aus der „Snowden-Affaire“ gelernt, agieren vorsichtiger und wissen ganz genau, dass die Menschen eine solche Meldung beunruhigen würde und vielleicht sogar zu einem Aufstand führen würde. In einer solchen Situation kann es sich niemand leisten. Deswegen spielt sich alles im Hintergrund ab – ohne das jemand etwas davon mitkriegt.
And who thinks, "Oh, no one in Germany will take part." - is wrong.
"In the fight against the further spread of the corona virus, Deutsche Telekom, for example, is already supplying anonymous location data of millions of German mobile phone users to the Robert Koch Institute.” (Jörn Brien 27.03.2020: „Keine Überwachung geplant: EU einigt sich mit Telekom-Riesen über Handydaten-Weitergabe, yeebase media GmbH)
All right, now some people are thinking "It's "just" metadata." Then go one step further in the direction of practice.
Which tools do you currently use in your company?
Many tools for video meetings or telephone conferences have American third party processors, and the "Big Five" are also listed frequently. How do I know that? Because we ourselves were recently looking for a secure video and telephone system. The same applies to various team chats - and just think what sensitive information can be quickly forwarded in a team chat. And then finally we come to our favourite topic - cloud storage and customer databases. In my opinion, this is where the risk potential is at its highest. Where else do you store your sensitive data if not in the cloud?
At this point I would like to emphasize that even if many providers advertise on their website with "Made in Germany" and "Maximum data protection", in many cases this is not 100% true. A quick look at the order processing contract and technical-organizational measures is usually sufficient.
You should pay special attention to free offers, because they are usually not really free of charge. Rather, there is a "currency exchange" behind them, where you do not pay for your products with money, but with your data. This way you are no longer a customer but the product - how else can providers of such services afford such offers economically? How often do you hear in the media "Company XY" sells data to ... .". Also recently, the media reported that a popular video meeting tool that many use in the business environment is reselling your data to a major American corporation. How much would your data be worth? Unfortunately, data monetization is "normal everyday life" for large corporations these days.

Are we ready for home work?
Many companies are currently in the process of sending their employees to the home office - without first checking their working environment.
Many home computers do not have sufficient or up-to-date anti-virus protection and are already "contaminated" without the owners knowing it.
Even digital tools designed to facilitate communication and work in the home office are selected too quickly - without the data protection officer first looking into the subcontracting relationships or the contract processing agreement. However, data protection is also an important issue in the home office. Even more so than in the (hopefully) protected office environment.
An example: Many parents are currently working from home and at the same time looking after their children - hats off! This is not easy in most cases. But what would happen if an employee went to the toilet for a short time - without prior data backup and screen lock and the unneeded child then gains access to the PC or laptop. Data is deleted, sent or moved too quickly. Would this have consequences for your company? Do you have a backup of data in case data is accidentally deleted?
There are many things to consider in such a situation.
Hackers exploit corona crisis - "Cyber-Corona"
The fear and insecurity of the population is shamelessly exploited by cyber criminals. Sites that collect information about the COVID-19 development have malicious software on them. Cyber criminals equip sites with spy software to monitor the users. Emails with information about the Corona crisis are also provided with malware, whereby users unknowingly download malware.
In such attacks, covert screenshots, video and audio recordings are made via connected cameras and microphones. It is not even visible to the user whether the device is switched on, e.g. flashing lights on cameras.
Such attacks give hackers access to sensitive information and data. This includes not only holiday photos, but also e-mails, passwords, chat content, financial and payment data.
I would like to remind you at this point that with such data not only identities can be stolen, but companies could also suffer economic consequences. For example, what if customer data or chat histories could suddenly be publicly available on the Internet.
Therefore always - especially now - be aware of what you click and download on the Internet or in emails, so that you do not get infected with "cyber corona". Because such "traps" can also be behind free webinars, e-books or "Corona special offers".

Home Office Checklist for a safe working environment
This checklist does not claim to be exhaustive, but it does show what we consider to be the most important questions that employers should ask themselves before blindly rushing themselves and their employees into the home office.
Are my employees allowed to work in the home office?
- Are personal data of customers processed at home?
- Check regulations in contract processing agreements
- prepare any necessary measures and obtain consent
- adapt technical-organizational measures if necessary
What digital tools do we need?
- Telephone system
- Video conference
- team chat
- Project Management Tool
- Cloud storage for secure data exchange
- Calendar
- Time recording
- Password Manager
- …
What are our demands on these tools?
- Server location Germany
- Client side encryption
- zero-knowledge principle
- Use of Open Source Software
- No subcontracting outside Germany
- German Support
- Flexible contract terms and rates
- Special features
- …
Are the employee workstations at home ready?
- Equipment: work equipment, headset, webcam
- Current updates and operating systems
- Stable internet connection
- Existing antivirus software/ firewall
- Lockable rooms
- …
Next step: Prepare your virtual team
Once the framework conditions have been clarified, nothing can really go wrong. But what about the implementation?
For many employees and managers it is an interesting situation, but one that takes some getting used to. Do all colleagues know how work is done? Who is responsible for what? Do their colleagues get along with the tools? Does everyone know how and when to work with the tools?
Here the old principle "communication is everything" clearly applies. It is essential that you discuss with your employees beforehand what you are planning and what difficulties may arise. Take away any fears of not understanding the technology in advance by assuring your employees that you also have to get used to everything first and that you yourself are no professional. Nothing hampers productivity more than employees who spend hours "trying out" because they don't dare to ask!
In this sense: Have courage and enjoy your work!
Author: Nicole Smuga
--
"Jörn Brien (27.03.2020): Edward Snowden: Jetzt errichtete Überwachung wird Corona-Krise überdauern."
"Sabina Wolf (19.03.2020): Coronavirus: Hacker nutzen Pandemie für Angriffe aus. Bayerischer Rundfunk."
"Michael Schäfer (27.3.2020): Videokonferenz-App: Zoom soll heimlich Daten an Facebook übermitteln. ComputerBase GmbH."
Coronavirus 5 point plan from luckycloud
-Home Office secure and successful implementation
Part 1:
The fastest and safest way to the home office
–
- Corona-Home Office Guide from luckycloud and the advantages of working from home
Part 2:
Corona crisis becomes surveillance affair 2.0
-Data protection checklist for digital tools
Part 3:
Working from home without loss of control
-Leading virtual teams digitally, independent of location
Part 4:
In 3 steps set up cloud storage in your home office with luckycloud
-Secure cloud storage from Germany for your home
Part 5:
Using cloud storage in the home office
- Exchange data securely and easily in a team with luckycloud
You might also be interested in

Switching Email Providers with Your Own Domain: What Matters
More and more freelancers and businesses are questioning whether their current email provider still meets their needs. And it’s rarely just about features or pricing. The focus is on control over y...
Updated: 20.01.2026
Learn more
Secure Exchange Alternative: Open-Source Groupware from Germany for Data-Sovereign Teams
More and more companies are reassessing whether their current communication systems still meet their needs. Proprietary platforms like Microsoft Exchange tie users to complex licensing models, rigi...
Updated: 15.10.2025
Learn more
Cloud Storage for Teams: Collaborate Securely, Flexibly, and GDPR-Compliant
A cloud storage solution for teams is indispensable today. Teamwork has long since gone digital: hybrid models and distributed locations are part of everyday life, files need to be available at all...
Updated: 01.10.2025
Learn more
Secure Dropbox Alternatives: Cloud Storage Compared
Dropbox is one of the most well-known cloud storage services worldwide, used by millions of people every day. But a closer look reveals a fundamental privacy issue behind its convenient interface....
Updated: 08.08.2025
Learn more
Cloud Infrastructure for Startups: How to Launch Securely and Scale Confidently
You've taken the first step: the company is founded, the team is motivated. Now you need a digital infrastructure that can keep up with your ideas. What’s often underestimated in practice: choosing...
Updated: 21.05.2025
Learn more
Host Europe migrates email to Microsoft – and SMEs lose data sovereignty
Host Europe has made its move: The provider has announced that all email mailboxes will be migrated to Microsoft 365 starting in May 2025. Anyone who previously trusted their data to servers in Ger...
Updated: 01.04.2025
Learn more
Secure Data Exchange with Clients Made Easy: One-Time Codes and Name Entry with luckycloud
Sharing data with others should be as simple and secure as possible. Companies need to exchange sensitive information with clients, partners, or internal teams—but once a link is shared, it can qui...
Updated: 26.03.2025
Learn more
Less Frustration, More Flow: A Comparison of the Most Popular Tools for Digital Collaboration
Digital communication and collaboration are essential in companies – but often feel more like chaos than productivity. We compare the most common tools and highlight their advantages and disadvanta...
Updated: 21.03.2025
Learn more
luckychat is here! The new open-source messenger from luckycloud for optimal team communication
From now on, luckychat is available as a secure open-source alternative to platforms like Microsoft Teams and Slack for your business! The latest addition to the luckycloud product family guarantee...
Updated: 29.01.2025
Learn more
Cloud and Collaboration Trends 2025: Security and Teamwork in Focus
The IT world is evolving faster than ever – staying ahead means being prepared. 2025 brings groundbreaking advancements in cloud security, hybrid cloud, and digital collaboration tools. Discover th...
Updated: 11.03.2025
Learn more
Secure Alternative to Webex, Zoom, and Co.: luckycloud Launches Solution for Online Meetings
Secure online meetings are a must-have, and video conferencing tools are indispensable in everyday work life. However, providers like Zoom or Webex are heavily criticized due to data privacy issues.
Updated: 11.03.2025
Learn more
Artificial intelligence in the enterprise: How humans and technology become a service dream team
Whether a customer remains loyal to a company or switches to a competitor is increasingly determined by contact with customer service. Today, consumers and business customers alike expect fast and...
Updated: 27.10.2023
Learn more
Protected data rooms: Cloud service for works councils ensures IT independence
Securely storing and processing their own data in the cloud is now part of everyday work for more and more companies. In recent years, they have increasingly introduced new systems, expanded intern...
Updated: 27.10.2023
Learn more
Digitalprämie Berlin - how to benefit from the subsidies with luckycloud
With the digital bonus, the state of Berlin and Investitionsbank Berlin (IBB) want to promote the digitalization of the working world. The acquisition of IT hardware and software for digital transf...
Updated: 07.06.2023
Learn more
Service for cloud solutions: Focus on the customer's needs
Good service pays off - this is also or especially true in difficult times, when the economy is facing numerous challenges due to the Corona pandemic. Only those who convince their customers with a...
Updated: 07.06.2023
Learn more
QNAP NAS and luckycloud - perfect match for Hybrid Clouds
Hybrid Cloud solutions do not have to be complicated. As with all successful combinations, it all depends on the right components! luckycloud - as a secure cloud provider from Germany with the high...
Updated: 07.06.2023
Learn more
All-rounder Hybrid Cloud - clever combination of backup and data processing
IT systems can be affected by failures or maintenance. During this time data in the cloud is not accessible. If you use the cloud storage as pure backup, a failure only affects current changes. But...
Updated: 22.06.2023
Learn more
Crash course GDPR - Summary of the 10 most important facts
25 May 2018 - the GDPR came into force on this date. Curse or blessing? After 2 years this is not exactly one of the most popular topics for companies. Nevertheless, the DSGVO has an important sign...
Updated: 07.06.2023
Learn more
Cloud storage in the home office - Set up luckycloud in your home office in 3 steps
There is hardly anyone left who is not affected by the current crisis, let alone severely restricted. Suddenly there are people in the home office who have never (had to) think about how to work ou...
Updated: 22.06.2023
Learn more
Home Office Preparation - Working from home without loss of control
Many managers are currently in conflict over the decision whether to use home office or not. The biggest barrier here is not the technical hurdle, but the feeling of loss of control. Many bosses ar...
Updated: 07.06.2023
Learn more
Home Office Checklist - Corona crisis becomes surveillance scandal 2.0
The corona crisis has stirred up many minds. Many entrepreneurs are interested in a quick solution and forget the daily dangers of digital data processing. People's privacy is sometimes trampled un...
Updated: 07.06.2023
Learn more
Home Office Guide in times of the coronavirus - working fast and safe from home
Current news about the corona virus is piling up. Many send their employees to the home office - but for many industries this is simply impossible. On various platforms there are lists of digital t...
Updated: 07.06.2023
Learn more
A cloud provider from Germany with easy user and data administration was especially important to us!
The demands for schools to be equipped with technical devices, a modern IT infrastructure and secure software solutions are anything but new. This applies to the administration as well as the teach...
Updated: 22.06.2023
Learn more
Why are updates important?
"Again?!", this is the thought you always have when you see a pop up with an update on your computer again. One is simply annoyed and clicks on "Remember later". But this is exactly what you should...
Updated: 07.06.2023
Learn more
Anniversary of the basic data protection regulation - Part 3 outlook and summary
Indeed, further regulations will follow in the future. With the DSGVO, the basic framework for far-reaching data protection regulation has been established, although the next stage of the DSGVO is...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 2 Travelling in the Cloud as a Business Customer
With the introduction of the DSGVO, the protection of personal data has rightly moved back to the foreground. In this part of the three-part interview with Fresh Compliance, we have clarified for y...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 1 What is the DSGVO?
One year has now passed since the DSGVO came into force and its introduction caused a lot of unrest and has been hotly debated in recent years, as has the topic of data protection in public clouds....
Updated: 07.06.2023
Learn more
Introduction to luckycloud - Part 2 Collaborative Teamwork with the Team Manager
One has just got used to the old system and then the boss comes around the corner and is of the opinion to integrate a new system because the old one is no longer DSGVO-compliant. The switch to a n...
Updated: 07.06.2023
Learn more
Switching Email Providers with Your Own Domain: What Matters
More and more freelancers and businesses are questioning whether their current email provider still meets their needs. And it’s rarely just about features or pricing. The focus is on control over y...
Updated: 20.01.2026
Learn more
Secure Exchange Alternative: Open-Source Groupware from Germany for Data-Sovereign Teams
More and more companies are reassessing whether their current communication systems still meet their needs. Proprietary platforms like Microsoft Exchange tie users to complex licensing models, rigi...
Updated: 15.10.2025
Learn more
Cloud Storage for Teams: Collaborate Securely, Flexibly, and GDPR-Compliant
A cloud storage solution for teams is indispensable today. Teamwork has long since gone digital: hybrid models and distributed locations are part of everyday life, files need to be available at all...
Updated: 01.10.2025
Learn more
Secure Dropbox Alternatives: Cloud Storage Compared
Dropbox is one of the most well-known cloud storage services worldwide, used by millions of people every day. But a closer look reveals a fundamental privacy issue behind its convenient interface....
Updated: 08.08.2025
Learn more
Cloud Infrastructure for Startups: How to Launch Securely and Scale Confidently
You've taken the first step: the company is founded, the team is motivated. Now you need a digital infrastructure that can keep up with your ideas. What’s often underestimated in practice: choosing...
Updated: 21.05.2025
Learn more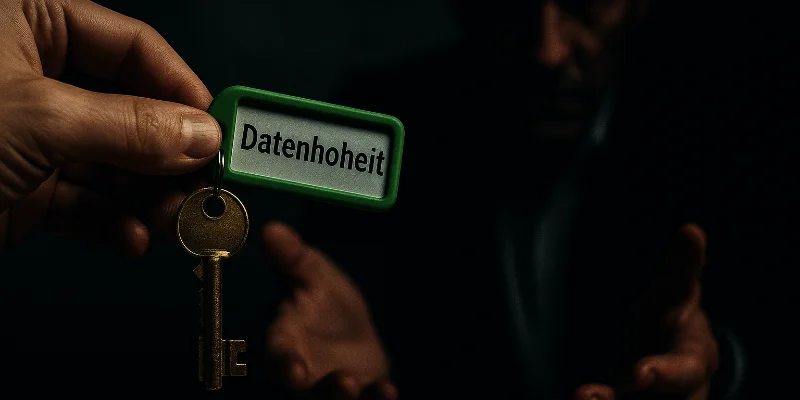
Host Europe migrates email to Microsoft – and SMEs lose data sovereignty
Host Europe has made its move: The provider has announced that all email mailboxes will be migrated to Microsoft 365 starting in May 2025. Anyone who previously trusted their data to servers in Ger...
Updated: 01.04.2025
Learn more
Secure Data Exchange with Clients Made Easy: One-Time Codes and Name Entry with luckycloud
Sharing data with others should be as simple and secure as possible. Companies need to exchange sensitive information with clients, partners, or internal teams—but once a link is shared, it can qui...
Updated: 26.03.2025
Learn more
Less Frustration, More Flow: A Comparison of the Most Popular Tools for Digital Collaboration
Digital communication and collaboration are essential in companies – but often feel more like chaos than productivity. We compare the most common tools and highlight their advantages and disadvanta...
Updated: 21.03.2025
Learn more
luckychat is here! The new open-source messenger from luckycloud for optimal team communication
From now on, luckychat is available as a secure open-source alternative to platforms like Microsoft Teams and Slack for your business! The latest addition to the luckycloud product family guarantee...
Updated: 29.01.2025
Learn more
Cloud and Collaboration Trends 2025: Security and Teamwork in Focus
The IT world is evolving faster than ever – staying ahead means being prepared. 2025 brings groundbreaking advancements in cloud security, hybrid cloud, and digital collaboration tools. Discover th...
Updated: 11.03.2025
Learn more
Secure Alternative to Webex, Zoom, and Co.: luckycloud Launches Solution for Online Meetings
Secure online meetings are a must-have, and video conferencing tools are indispensable in everyday work life. However, providers like Zoom or Webex are heavily criticized due to data privacy issues.
Updated: 11.03.2025
Learn more
Artificial intelligence in the enterprise: How humans and technology become a service dream team
Whether a customer remains loyal to a company or switches to a competitor is increasingly determined by contact with customer service. Today, consumers and business customers alike expect fast and...
Updated: 27.10.2023
Learn more
Protected data rooms: Cloud service for works councils ensures IT independence
Securely storing and processing their own data in the cloud is now part of everyday work for more and more companies. In recent years, they have increasingly introduced new systems, expanded intern...
Updated: 27.10.2023
Learn more
Digitalprämie Berlin - how to benefit from the subsidies with luckycloud
With the digital bonus, the state of Berlin and Investitionsbank Berlin (IBB) want to promote the digitalization of the working world. The acquisition of IT hardware and software for digital transf...
Updated: 07.06.2023
Learn more
Service for cloud solutions: Focus on the customer's needs
Good service pays off - this is also or especially true in difficult times, when the economy is facing numerous challenges due to the Corona pandemic. Only those who convince their customers with a...
Updated: 07.06.2023
Learn more
QNAP NAS and luckycloud - perfect match for Hybrid Clouds
Hybrid Cloud solutions do not have to be complicated. As with all successful combinations, it all depends on the right components! luckycloud - as a secure cloud provider from Germany with the high...
Updated: 07.06.2023
Learn more
All-rounder Hybrid Cloud - clever combination of backup and data processing
IT systems can be affected by failures or maintenance. During this time data in the cloud is not accessible. If you use the cloud storage as pure backup, a failure only affects current changes. But...
Updated: 22.06.2023
Learn more
Crash course GDPR - Summary of the 10 most important facts
25 May 2018 - the GDPR came into force on this date. Curse or blessing? After 2 years this is not exactly one of the most popular topics for companies. Nevertheless, the DSGVO has an important sign...
Updated: 07.06.2023
Learn more
Cloud storage in the home office - Set up luckycloud in your home office in 3 steps
There is hardly anyone left who is not affected by the current crisis, let alone severely restricted. Suddenly there are people in the home office who have never (had to) think about how to work ou...
Updated: 22.06.2023
Learn more
Home Office Preparation - Working from home without loss of control
Many managers are currently in conflict over the decision whether to use home office or not. The biggest barrier here is not the technical hurdle, but the feeling of loss of control. Many bosses ar...
Updated: 07.06.2023
Learn more
Home Office Checklist - Corona crisis becomes surveillance scandal 2.0
The corona crisis has stirred up many minds. Many entrepreneurs are interested in a quick solution and forget the daily dangers of digital data processing. People's privacy is sometimes trampled un...
Updated: 07.06.2023
Learn more
Home Office Guide in times of the coronavirus - working fast and safe from home
Current news about the corona virus is piling up. Many send their employees to the home office - but for many industries this is simply impossible. On various platforms there are lists of digital t...
Updated: 07.06.2023
Learn more
A cloud provider from Germany with easy user and data administration was especially important to us!
The demands for schools to be equipped with technical devices, a modern IT infrastructure and secure software solutions are anything but new. This applies to the administration as well as the teach...
Updated: 22.06.2023
Learn more
Why are updates important?
"Again?!", this is the thought you always have when you see a pop up with an update on your computer again. One is simply annoyed and clicks on "Remember later". But this is exactly what you should...
Updated: 07.06.2023
Learn more
Anniversary of the basic data protection regulation - Part 3 outlook and summary
Indeed, further regulations will follow in the future. With the DSGVO, the basic framework for far-reaching data protection regulation has been established, although the next stage of the DSGVO is...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 2 Travelling in the Cloud as a Business Customer
With the introduction of the DSGVO, the protection of personal data has rightly moved back to the foreground. In this part of the three-part interview with Fresh Compliance, we have clarified for y...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 1 What is the DSGVO?
One year has now passed since the DSGVO came into force and its introduction caused a lot of unrest and has been hotly debated in recent years, as has the topic of data protection in public clouds....
Updated: 07.06.2023
Learn more
Introduction to luckycloud - Part 2 Collaborative Teamwork with the Team Manager
One has just got used to the old system and then the boss comes around the corner and is of the opinion to integrate a new system because the old one is no longer DSGVO-compliant. The switch to a n...
Updated: 07.06.2023
Learn more
Switching Email Providers with Your Own Domain: What Matters
More and more freelancers and businesses are questioning whether their current email provider still meets their needs. And it’s rarely just about features or pricing. The focus is on control over y...
Updated: 20.01.2026
Learn more
Secure Exchange Alternative: Open-Source Groupware from Germany for Data-Sovereign Teams
More and more companies are reassessing whether their current communication systems still meet their needs. Proprietary platforms like Microsoft Exchange tie users to complex licensing models, rigi...
Updated: 15.10.2025
Learn more
Cloud Storage for Teams: Collaborate Securely, Flexibly, and GDPR-Compliant
A cloud storage solution for teams is indispensable today. Teamwork has long since gone digital: hybrid models and distributed locations are part of everyday life, files need to be available at all...
Updated: 01.10.2025
Learn more
Secure Dropbox Alternatives: Cloud Storage Compared
Dropbox is one of the most well-known cloud storage services worldwide, used by millions of people every day. But a closer look reveals a fundamental privacy issue behind its convenient interface....
Updated: 08.08.2025
Learn more
Cloud Infrastructure for Startups: How to Launch Securely and Scale Confidently
You've taken the first step: the company is founded, the team is motivated. Now you need a digital infrastructure that can keep up with your ideas. What’s often underestimated in practice: choosing...
Updated: 21.05.2025
Learn more
Host Europe migrates email to Microsoft – and SMEs lose data sovereignty
Host Europe has made its move: The provider has announced that all email mailboxes will be migrated to Microsoft 365 starting in May 2025. Anyone who previously trusted their data to servers in Ger...
Updated: 01.04.2025
Learn more
Secure Data Exchange with Clients Made Easy: One-Time Codes and Name Entry with luckycloud
Sharing data with others should be as simple and secure as possible. Companies need to exchange sensitive information with clients, partners, or internal teams—but once a link is shared, it can qui...
Updated: 26.03.2025
Learn more
Less Frustration, More Flow: A Comparison of the Most Popular Tools for Digital Collaboration
Digital communication and collaboration are essential in companies – but often feel more like chaos than productivity. We compare the most common tools and highlight their advantages and disadvanta...
Updated: 21.03.2025
Learn more
luckychat is here! The new open-source messenger from luckycloud for optimal team communication
From now on, luckychat is available as a secure open-source alternative to platforms like Microsoft Teams and Slack for your business! The latest addition to the luckycloud product family guarantee...
Updated: 29.01.2025
Learn more
Cloud and Collaboration Trends 2025: Security and Teamwork in Focus
The IT world is evolving faster than ever – staying ahead means being prepared. 2025 brings groundbreaking advancements in cloud security, hybrid cloud, and digital collaboration tools. Discover th...
Updated: 11.03.2025
Learn more
Secure Alternative to Webex, Zoom, and Co.: luckycloud Launches Solution for Online Meetings
Secure online meetings are a must-have, and video conferencing tools are indispensable in everyday work life. However, providers like Zoom or Webex are heavily criticized due to data privacy issues.
Updated: 11.03.2025
Learn more
Artificial intelligence in the enterprise: How humans and technology become a service dream team
Whether a customer remains loyal to a company or switches to a competitor is increasingly determined by contact with customer service. Today, consumers and business customers alike expect fast and...
Updated: 27.10.2023
Learn more
Protected data rooms: Cloud service for works councils ensures IT independence
Securely storing and processing their own data in the cloud is now part of everyday work for more and more companies. In recent years, they have increasingly introduced new systems, expanded intern...
Updated: 27.10.2023
Learn more
Digitalprämie Berlin - how to benefit from the subsidies with luckycloud
With the digital bonus, the state of Berlin and Investitionsbank Berlin (IBB) want to promote the digitalization of the working world. The acquisition of IT hardware and software for digital transf...
Updated: 07.06.2023
Learn more
Service for cloud solutions: Focus on the customer's needs
Good service pays off - this is also or especially true in difficult times, when the economy is facing numerous challenges due to the Corona pandemic. Only those who convince their customers with a...
Updated: 07.06.2023
Learn more
QNAP NAS and luckycloud - perfect match for Hybrid Clouds
Hybrid Cloud solutions do not have to be complicated. As with all successful combinations, it all depends on the right components! luckycloud - as a secure cloud provider from Germany with the high...
Updated: 07.06.2023
Learn more
All-rounder Hybrid Cloud - clever combination of backup and data processing
IT systems can be affected by failures or maintenance. During this time data in the cloud is not accessible. If you use the cloud storage as pure backup, a failure only affects current changes. But...
Updated: 22.06.2023
Learn more
Crash course GDPR - Summary of the 10 most important facts
25 May 2018 - the GDPR came into force on this date. Curse or blessing? After 2 years this is not exactly one of the most popular topics for companies. Nevertheless, the DSGVO has an important sign...
Updated: 07.06.2023
Learn more
Cloud storage in the home office - Set up luckycloud in your home office in 3 steps
There is hardly anyone left who is not affected by the current crisis, let alone severely restricted. Suddenly there are people in the home office who have never (had to) think about how to work ou...
Updated: 22.06.2023
Learn more
Home Office Preparation - Working from home without loss of control
Many managers are currently in conflict over the decision whether to use home office or not. The biggest barrier here is not the technical hurdle, but the feeling of loss of control. Many bosses ar...
Updated: 07.06.2023
Learn more
Home Office Checklist - Corona crisis becomes surveillance scandal 2.0
The corona crisis has stirred up many minds. Many entrepreneurs are interested in a quick solution and forget the daily dangers of digital data processing. People's privacy is sometimes trampled un...
Updated: 07.06.2023
Learn more
Home Office Guide in times of the coronavirus - working fast and safe from home
Current news about the corona virus is piling up. Many send their employees to the home office - but for many industries this is simply impossible. On various platforms there are lists of digital t...
Updated: 07.06.2023
Learn more
A cloud provider from Germany with easy user and data administration was especially important to us!
The demands for schools to be equipped with technical devices, a modern IT infrastructure and secure software solutions are anything but new. This applies to the administration as well as the teach...
Updated: 22.06.2023
Learn more
Why are updates important?
"Again?!", this is the thought you always have when you see a pop up with an update on your computer again. One is simply annoyed and clicks on "Remember later". But this is exactly what you should...
Updated: 07.06.2023
Learn more
Anniversary of the basic data protection regulation - Part 3 outlook and summary
Indeed, further regulations will follow in the future. With the DSGVO, the basic framework for far-reaching data protection regulation has been established, although the next stage of the DSGVO is...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 2 Travelling in the Cloud as a Business Customer
With the introduction of the DSGVO, the protection of personal data has rightly moved back to the foreground. In this part of the three-part interview with Fresh Compliance, we have clarified for y...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 1 What is the DSGVO?
One year has now passed since the DSGVO came into force and its introduction caused a lot of unrest and has been hotly debated in recent years, as has the topic of data protection in public clouds....
Updated: 07.06.2023
Learn more
Introduction to luckycloud - Part 2 Collaborative Teamwork with the Team Manager
One has just got used to the old system and then the boss comes around the corner and is of the opinion to integrate a new system because the old one is no longer DSGVO-compliant. The switch to a n...
Updated: 07.06.2023
Learn more
Switching Email Providers with Your Own Domain: What Matters
More and more freelancers and businesses are questioning whether their current email provider still meets their needs. And it’s rarely just about features or pricing. The focus is on control over y...
Updated: 20.01.2026
Learn more
Secure Exchange Alternative: Open-Source Groupware from Germany for Data-Sovereign Teams
More and more companies are reassessing whether their current communication systems still meet their needs. Proprietary platforms like Microsoft Exchange tie users to complex licensing models, rigi...
Updated: 15.10.2025
Learn more
Cloud Storage for Teams: Collaborate Securely, Flexibly, and GDPR-Compliant
A cloud storage solution for teams is indispensable today. Teamwork has long since gone digital: hybrid models and distributed locations are part of everyday life, files need to be available at all...
Updated: 01.10.2025
Learn more
Secure Dropbox Alternatives: Cloud Storage Compared
Dropbox is one of the most well-known cloud storage services worldwide, used by millions of people every day. But a closer look reveals a fundamental privacy issue behind its convenient interface....
Updated: 08.08.2025
Learn more
Cloud Infrastructure for Startups: How to Launch Securely and Scale Confidently
You've taken the first step: the company is founded, the team is motivated. Now you need a digital infrastructure that can keep up with your ideas. What’s often underestimated in practice: choosing...
Updated: 21.05.2025
Learn more
Host Europe migrates email to Microsoft – and SMEs lose data sovereignty
Host Europe has made its move: The provider has announced that all email mailboxes will be migrated to Microsoft 365 starting in May 2025. Anyone who previously trusted their data to servers in Ger...
Updated: 01.04.2025
Learn more
Secure Data Exchange with Clients Made Easy: One-Time Codes and Name Entry with luckycloud
Sharing data with others should be as simple and secure as possible. Companies need to exchange sensitive information with clients, partners, or internal teams—but once a link is shared, it can qui...
Updated: 26.03.2025
Learn more
Less Frustration, More Flow: A Comparison of the Most Popular Tools for Digital Collaboration
Digital communication and collaboration are essential in companies – but often feel more like chaos than productivity. We compare the most common tools and highlight their advantages and disadvanta...
Updated: 21.03.2025
Learn more
luckychat is here! The new open-source messenger from luckycloud for optimal team communication
From now on, luckychat is available as a secure open-source alternative to platforms like Microsoft Teams and Slack for your business! The latest addition to the luckycloud product family guarantee...
Updated: 29.01.2025
Learn more
Cloud and Collaboration Trends 2025: Security and Teamwork in Focus
The IT world is evolving faster than ever – staying ahead means being prepared. 2025 brings groundbreaking advancements in cloud security, hybrid cloud, and digital collaboration tools. Discover th...
Updated: 11.03.2025
Learn more
Secure Alternative to Webex, Zoom, and Co.: luckycloud Launches Solution for Online Meetings
Secure online meetings are a must-have, and video conferencing tools are indispensable in everyday work life. However, providers like Zoom or Webex are heavily criticized due to data privacy issues.
Updated: 11.03.2025
Learn more
Artificial intelligence in the enterprise: How humans and technology become a service dream team
Whether a customer remains loyal to a company or switches to a competitor is increasingly determined by contact with customer service. Today, consumers and business customers alike expect fast and...
Updated: 27.10.2023
Learn more
Protected data rooms: Cloud service for works councils ensures IT independence
Securely storing and processing their own data in the cloud is now part of everyday work for more and more companies. In recent years, they have increasingly introduced new systems, expanded intern...
Updated: 27.10.2023
Learn more
Digitalprämie Berlin - how to benefit from the subsidies with luckycloud
With the digital bonus, the state of Berlin and Investitionsbank Berlin (IBB) want to promote the digitalization of the working world. The acquisition of IT hardware and software for digital transf...
Updated: 07.06.2023
Learn more
Service for cloud solutions: Focus on the customer's needs
Good service pays off - this is also or especially true in difficult times, when the economy is facing numerous challenges due to the Corona pandemic. Only those who convince their customers with a...
Updated: 07.06.2023
Learn more
QNAP NAS and luckycloud - perfect match for Hybrid Clouds
Hybrid Cloud solutions do not have to be complicated. As with all successful combinations, it all depends on the right components! luckycloud - as a secure cloud provider from Germany with the high...
Updated: 07.06.2023
Learn more
All-rounder Hybrid Cloud - clever combination of backup and data processing
IT systems can be affected by failures or maintenance. During this time data in the cloud is not accessible. If you use the cloud storage as pure backup, a failure only affects current changes. But...
Updated: 22.06.2023
Learn more
Crash course GDPR - Summary of the 10 most important facts
25 May 2018 - the GDPR came into force on this date. Curse or blessing? After 2 years this is not exactly one of the most popular topics for companies. Nevertheless, the DSGVO has an important sign...
Updated: 07.06.2023
Learn more
Cloud storage in the home office - Set up luckycloud in your home office in 3 steps
There is hardly anyone left who is not affected by the current crisis, let alone severely restricted. Suddenly there are people in the home office who have never (had to) think about how to work ou...
Updated: 22.06.2023
Learn more
Home Office Preparation - Working from home without loss of control
Many managers are currently in conflict over the decision whether to use home office or not. The biggest barrier here is not the technical hurdle, but the feeling of loss of control. Many bosses ar...
Updated: 07.06.2023
Learn more
Home Office Checklist - Corona crisis becomes surveillance scandal 2.0
The corona crisis has stirred up many minds. Many entrepreneurs are interested in a quick solution and forget the daily dangers of digital data processing. People's privacy is sometimes trampled un...
Updated: 07.06.2023
Learn more
Home Office Guide in times of the coronavirus - working fast and safe from home
Current news about the corona virus is piling up. Many send their employees to the home office - but for many industries this is simply impossible. On various platforms there are lists of digital t...
Updated: 07.06.2023
Learn more
A cloud provider from Germany with easy user and data administration was especially important to us!
The demands for schools to be equipped with technical devices, a modern IT infrastructure and secure software solutions are anything but new. This applies to the administration as well as the teach...
Updated: 22.06.2023
Learn more
Why are updates important?
"Again?!", this is the thought you always have when you see a pop up with an update on your computer again. One is simply annoyed and clicks on "Remember later". But this is exactly what you should...
Updated: 07.06.2023
Learn more
Anniversary of the basic data protection regulation - Part 3 outlook and summary
Indeed, further regulations will follow in the future. With the DSGVO, the basic framework for far-reaching data protection regulation has been established, although the next stage of the DSGVO is...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 2 Travelling in the Cloud as a Business Customer
With the introduction of the DSGVO, the protection of personal data has rightly moved back to the foreground. In this part of the three-part interview with Fresh Compliance, we have clarified for y...
Updated: 07.06.2023
Learn more
Anniversary of the Basic Data Protection Regulation - Part 1 What is the DSGVO?
One year has now passed since the DSGVO came into force and its introduction caused a lot of unrest and has been hotly debated in recent years, as has the topic of data protection in public clouds....
Updated: 07.06.2023
Learn more
Introduction to luckycloud - Part 2 Collaborative Teamwork with the Team Manager
One has just got used to the old system and then the boss comes around the corner and is of the opinion to integrate a new system because the old one is no longer DSGVO-compliant. The switch to a n...
Updated: 07.06.2023
Learn more